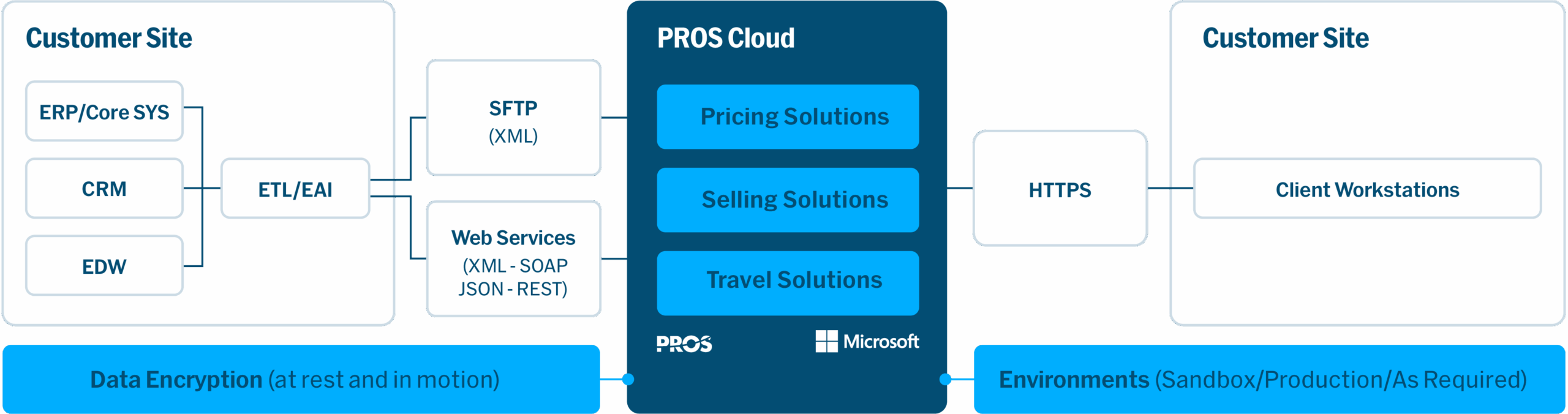
PROS Cloud
Secure Cloud Solutions you can rely on
Delivered globally under a Software-as-a-Service (SaaS) model hosted on Microsoft Azure
Communicates securely with your existing IT infrastructure
For a subscription fee, PROS provides access to PROS applications via a secure internet connection. This approach frees your IT team from the challenges associated with managing, maintaining and funding a scalable, secure and high-performance IT infrastructure.
In a modern enterprise IT setting, there will often be multiple IT system environments in use. PROS can provide environments to match your unique needs.
PROS Data Centers
PROS positions its data centers in optimal geographic locations to minimize latency and observe local legislative requirements. PROS data centers are deployed in primary and secondary pairs for backup and failover.
We utilize strategically positioned data centers within the Global Microsoft Azure network. There are currently PROS data center pairs in the Americas, northern and central Europe, and Australia, with further locations planned. We regularly evaluate data center expansion to enhance services for our global customers.


Scalability, Elasticity, and Resilience
PROS Cloud is built on Microsoft Azure and specifically configured with elasticity to scale to meet your performance requirements.
We’ve architected our SaaS solution to be highly available:
- Azure’s hyperscale data centers offer a wide range of resilient, secure, compliant, performant, and sustainable services
- Secondary data centers receive data backups
- A secondary data center is located at least 150 miles (240 km) away from the primary for high availability
- There is automated failover from the secondary data center in event of primary data center loss
The PROS Cloud team performs weekly full and daily incremental backups. PROS has a defined Recovery Point Objective (RPO) and Recovery Time Objective (RTO) for each solution. Scheduled backups are audited regularly and restore functionality is tested periodically to support disaster recovery planning.
Product support is a vital part of the total PROS customer experience. We’re dedicated to ensuring issues are resolved to your full satisfaction. Contact your PROS representative for details on our suite of product support offerings.


Responsive Operations and Support
Rigorous Approach
PROS Cloud environments are managed using industry standard processes. We’re rigorous and responsive to ensure the health of your environments. When we plan to make changes to deployments, a detailed change request is created that includes the impacted environment, implementation, rollback, verification, and customer communication procedures.
DevOps
We operate on a DevOps support model, so all the business functions that design, develop, deploy and support PROS solutions are in a single, coordinated organization.
Proactive Support Team
The PROS Cloud operations support team monitors systems activity to predict peaks in demand and then responds quickly and decisively to minimize operational impact.
Disaster Recovery
Business Continuity
Crisis Management
Corporate Readiness Plans
Leadership
Emergency Communication Channels
Cloud Continuity
Cloud Operations
Support Teams
Customer Notifications
Disaster Recovery
Environment Recovery
Service Recovery
Automated Recovery
Periodic Testing
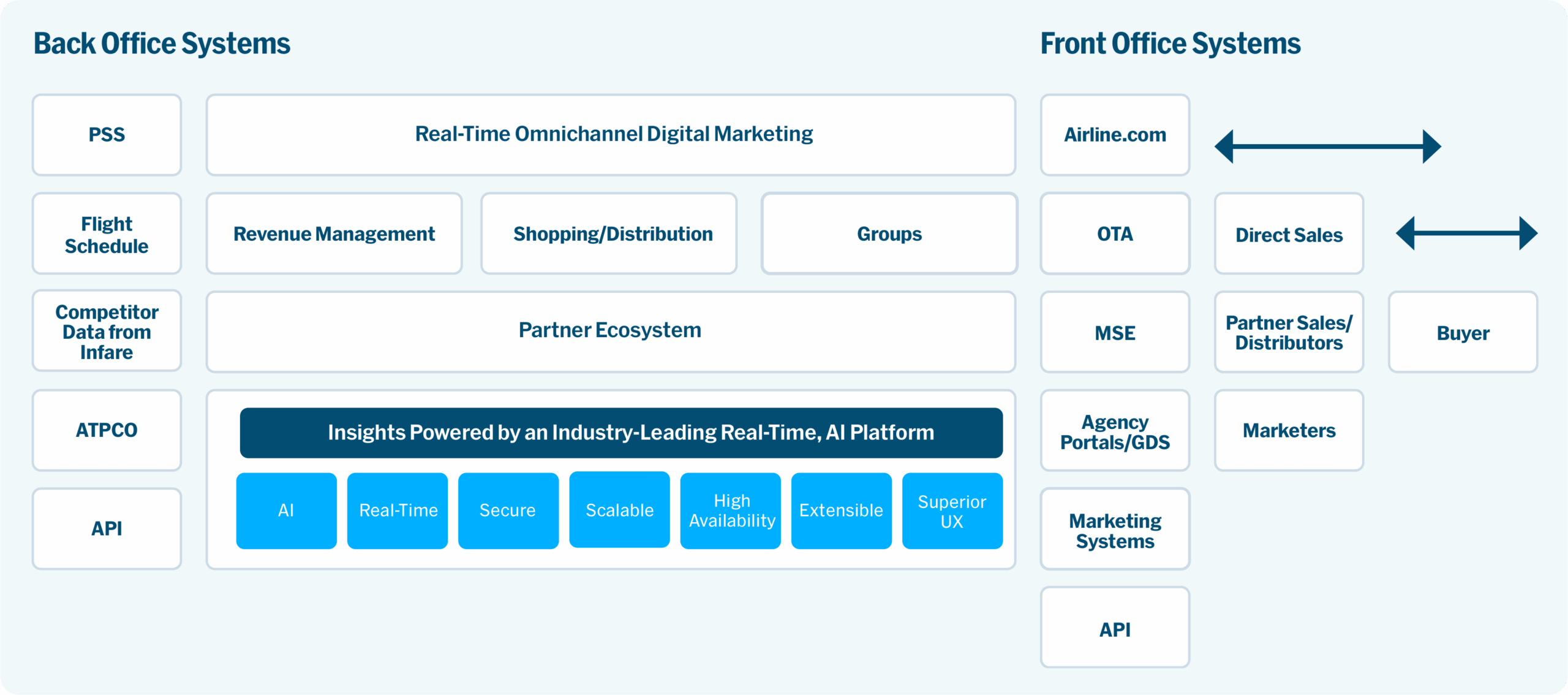
Flexible Integration
PROS application supports NDC and other standard APIs like IATA PAOREQ, PAORES, and other interfaces from EDIFACT allowing the PROS Solution to seamlessly integrate with GDS, OTA, Metasearch, Travel Agencies, etc.
Internal Integration
- Industry-standard web services (SOAP/REST) and XML files move data between PROS and external applications.
- APIs are secure over HTTPS and follow JSON protocols.
Security Management Program
Certifications and Compliance
Security is central to PROS culture. PROS is compliant with the General Data Protection Regulation (GDPR) and we annually undergo independent third-party audits for compliance with:
- SSAE16 SOC 2 Type 2
- ISO 27001
- ISO 27018
- CSA Cloud Control Matrix
Threat Protection Progams
We have an established security program to protect the confidentiality and integrity of information and services from anticipated threats of unauthorized or unlawful disclosure, modification, loss, or destruction of information. PROS Security Council performs regular gap assessments and executes initiatives to cover identified gaps.
Continued Enhancement
PROS solutions are subject to continual development to protect and enhance your investment. Functionality patches and minor enhancements are released and applied monthly while version upgrades occur every two months. Security patches are applied quickly to address any potential gaps.
PROS Information Security Management System
The PROS Information Security Management System is governed by a Security Council responsible for oversight and enforcement of comprehensive written security policies specifying:
- Enterprise-wide security awareness training
- Logical and physical security access control
- Environmental and physical security
- Incident response & disaster recovery; and more
The PROS Information Security Management System was designed and implemented in alignment with the requirements of ISO 27001. It includes policies, standards, guidelines and procedures for managing PROS information security.

Capabilities
PROS Applications, Designed Securely from the Start
Infrastructure
Highly Available, Scalable Platform
Infrastructure Optimized for PROS Apps
Secure Architecture with State-of-the-Art Defenses Against Cyber Attacks
Microsoft Azure/SOC 2/ISO 27001
Operating System
System Admin
OS Patching and Upgrade
DB Management
Data Protection: Backup and Recovery
Application Management
Application Health Check and Monitoring
Application Tuning and Optimization
Product Patching and Update
PROS development teams utilize Secure Development Lifecycle (SDLC) processes and perform rigorous testing to ensure security.
- Base PROS SDLC on OWASP industry best practices and tailor to the Agile methodology
- Perform Threat Modelling to identify and model security threats
- Complete Static Analysis Security Testing at the code level to identify vulnerabilities early
- Execute Dynamic Analysis Security Testing at the Web App level to identify vulnerabilities
- Conduct Final Security Review of all security activities performed on the application prior to release
- Run regular Vulnerability Scanning and manual Penetration Testing within the PROS solution
State-of-the-art Security Infrastructure
PROS deploys a state-of-the-art network security infrastructure. We utilize firewall and Intrusion Prevention System technologies to analyze network traffic and guard against attacks. For Host Security, PROS deploys an advanced antimalware solution that uses a pure machine learning approach to determine malicious activity. The solution can detect threats without relying on signature-based technology and techniques. A sophisticated host-based incident response tool hunts and captures threat activity in almost real time in conjunction with a powerful tool that can model and track the introduction of known good changes in systems and protect from non-trusted changes.
User Authentication
PROS Best Practice approach for installations is to leverage our customers’ current corporate identity management solution. Single Sign On (SSO) is the PROS preferred method. Where an SSO approach is used to integrate to an existing application infrastructure, we can leverage the Security Assertion Markup Language standard (SAML 2.0) as well as Microsoft Azure Active Directory.
Data Encryption
All data at rest is encrypted with an AES 256bit cipher. Data in motion is sent over HTTPS and TLS 1.2 where possible and again encrypted with an AES 256bit cipher. Encryption keys are held and protected as per key management best practices.
Additional Resources
PROS Trust & Security
- read more
PROS Named CSO Award Winner for Second Consecutive Year
- read more
PROS Recognized for Cybersecurity Excellence
PROS Chief Information Security Officer, explains that to be resilient and defend against the new breed of cyber threats requires security to become part of the organizational culture.
- read more